To celebrate World Password Day, we have revisited some research we conducted last year to understand how the password landscape has evolved over the last 12 months. How have the password habits of IT decision makers in the UK and US shifted? What impact does this have on both their personal and working life?
Before we start… what is World Password Day? Held every year on the first Thursday in May, it aims to highlight the importance of password security and promote best practice. Cyber criminals grow smarter every day and have a number of different attack types up their sleeves in order to gain access to password information, including keylogger attacks, credential stuffing and phishing. Considering the sheer number of cyber-attacks that take place every day and that fact that a recent report from Verizon found that 85% of breaches involved a human element, it is crucially important, not just for individuals but organisations as well, to ensure that password best practice is followed.
We surveyed 300 IT decision makers from enterprise organisations across the US and UK, revisiting some of the questions posed this time last year as well as some new ones, in order to understand how they approach password protection and what alternatives they might be looking to use.
Common sources of password inspiration could be more secure
Last year, only 17% of respondents reported that they always use a random password generator – typically believed to be among the most secure methods – but interestingly, that’s dropped to just 9% this year. The use of such tools continues to be more prevalent in the UK (19%) than the US (5%), but the percentages are still low across both markets. Such a decline is of course noteworthy with personal and organisational security in mind, but it may also be linked to the ever-growing access to, and use of, non-password authentication methods such as biometrics – more on that a bit later.
So, what else is more commonly used for password inspiration? Respondents instead favour thinking of something random themselves (39%) or using other potentially discoverable sources including: names of family members/friends (34%), memorable dates (32%) or TV and film (26%).
Password blunders could be leaving organisations vulnerable to attack and eroding confidence in the importance of a strong password leading to a false sense of security
When it comes to making password errors, the biggest mistakes being reported include recycling the same passwords (56%), leaving passwords in an obvious place to be found (44%) and that passwords are just too familiar (44%). That last stat stands in contrast to our earlier findings about sources of password ideas and perhaps highlights a paradox when it comes to passwords: people generally know what they need to do to be secure, but for many the lure and convenience of memorable passwords often wins out.
When comparing between US and UK respondents, those from the US chose an average of 4 mistakes while their UK counterparts are choosing an average of 3. In identifying more potential risks, it suggests that ITDMs in the US may be slightly more attuned to the many pitfalls of password errors.
To add to this, confidence levels continue to be low. Only just over a third (37%) of respondents are super confident that most employees are aware of the importance of a strong password and stick to best practices as much as possible, a trend which was also noted last year. US respondents feel much more confident (48%) in this area than their UK counterparts (17%), further echoing the point that ITDMs in US seem more focused on this area, perhaps rolling out training for staff members across their organisation. Whether this training is being adhered to is another matter.
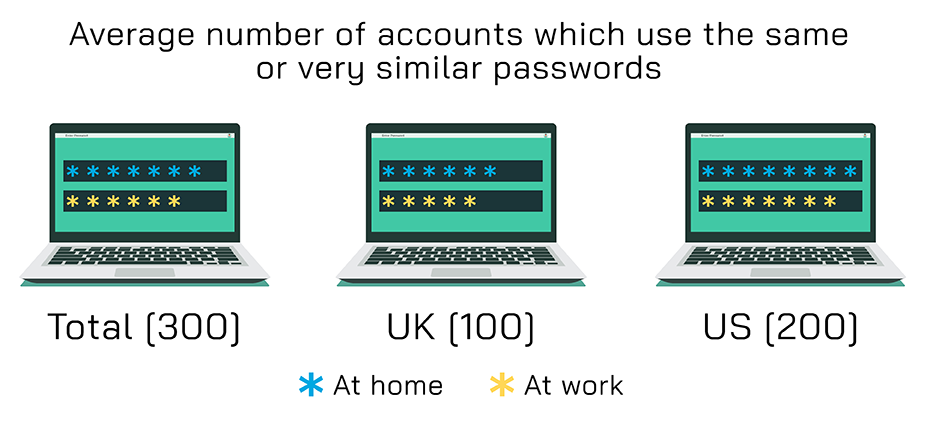
Again, highlighting our paradox, despite seemingly being aware of the risks, convenience seems to be the priority – surveyed respondents admitted that on average they use the same or very similar passwords for 6 different accounts at work, 7 when thinking about personal accounts. Even though ITDMs in the US seem more aware of the likely password errors, they are more likely to admit to recycling the passwords across accounts, both at work and at home, which is the top password error identified by respondents.
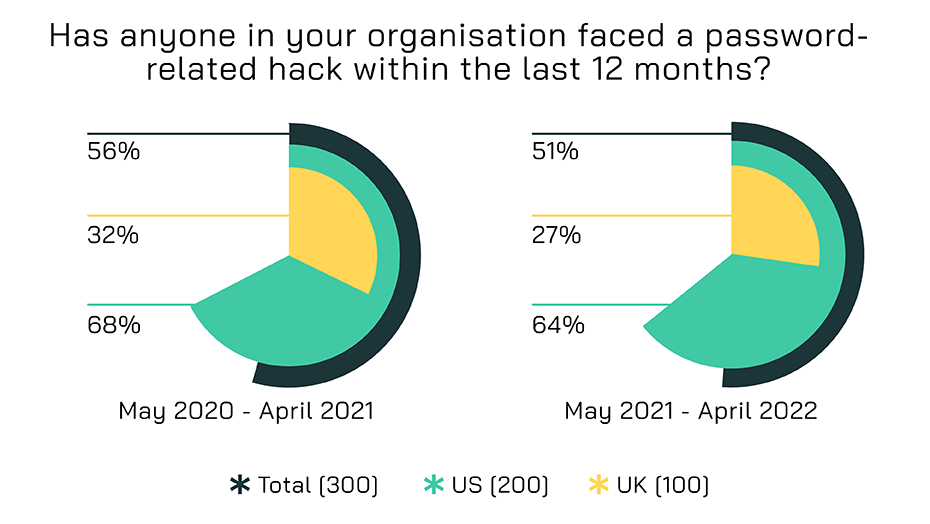
While direct experience of password related hacks has dropped, most have still witnessed them happening to their organisation
While it is encouraging to see that overall, the number of respondents reporting that someone in their organisation has faced a password-related hack in the last 12 months is decreasing, the majority still report that such an event has taken place – and that’s just the ones they’ve heard about. Those in the US continue to be much more likely to have faced one, which could be a driving reason why they have a higher awareness of the risks in this area.
On the surface, these year-on-year trends are going in the right direction but there is obviously still work to do in order for organisations to feel completely confident that staff will follow the protocols set out for them. And of course, they cannot afford to rest on their laurels, with cybercriminals constantly looking to develop ever-more sophisticated attack methods as they probe for weak spots in defences.
Passwords remain prevalent, but biometrics continue to boom
The use of passwords or phrases have been around for thousands of years and in the eyes of our respondents, continue to be the best way to secure both personal and work e-mail, as well as social media.
However, when it comes to online banking, respondents feel that using biometric data (including retina scan, facial recognition, and fingerprints) to secure access is best.
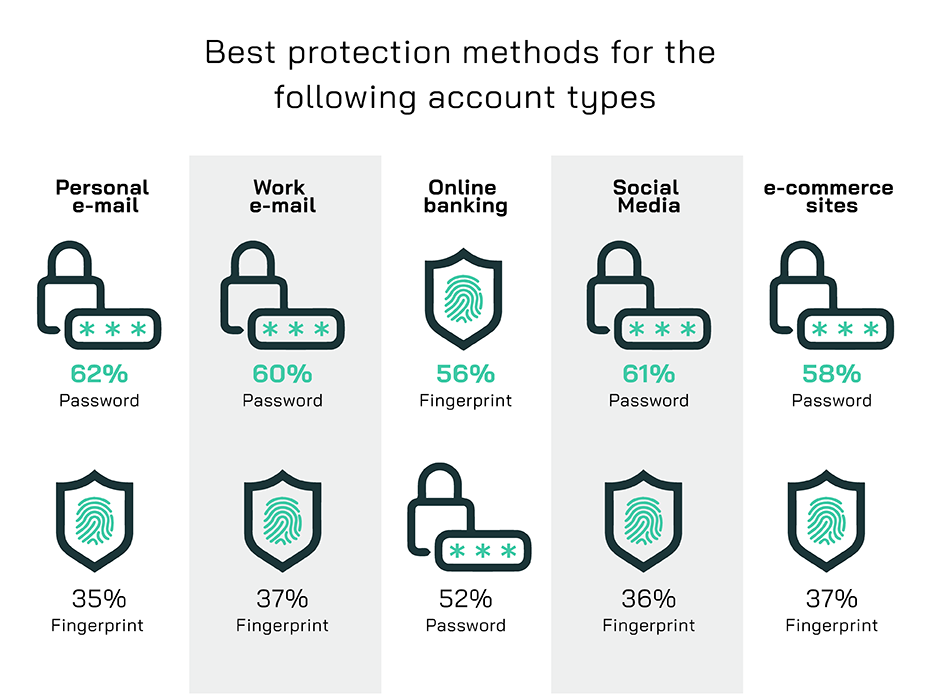
In fact, fingerprint is the most likely (64%) method ITDMs cite using alongside passwords, either personal or at work, to secure access to password protected areas like websites, online banking, and social media.
This could be due to the rise in access to such tools via mobile technology. By using a mobile device like a phone or tablet, users have a number of different options available to them to securely access their most personal data, and what is more personal than access to their online banking.
Biometric data is being used in many different settings (in the airport for example – in order to get through border control). Their use is arguably safer than passwords, as they are much harder to hack or steal. This bodes well for our surveyed ITDMs, with the vast majority (94%) reporting they have had to reset a password because they have forgotten it. Over half (56%) do so on a quarterly basis. The use of biometric data would help reduce this, but this protection method is not infallible, and hackers are quickly finding ways to steal this information too.
It’s clear that passwords aren’t being made obsolete just yet, but organisations should be investigating and investing in security solutions which explore the use of other secure access methods, in order to keep their most valuable IP safe and secure.
Methodology
300 IT decision makers from across the US and UK were interviewed in April 2022. All respondents were from organisations in the private sector, with 1,000 or more employees.